11 things about Network Security by MaxSecure
1. Attacks on your network can cause your personal information like passwords, banking details and other private data to be exposed.
2. ARP spoofing attacks can only occur on local area networks that utilize the Address Resolution Protocol.
3. ARP spoofing is a type of attack in which a malicious actor sends falsified ARP (Address Resolution Protocol) messages over a local area network.
4. Man-in-the-middle attacks: MITM attacks can rely on ARP spoofing to intercept and modify traffic between victims.
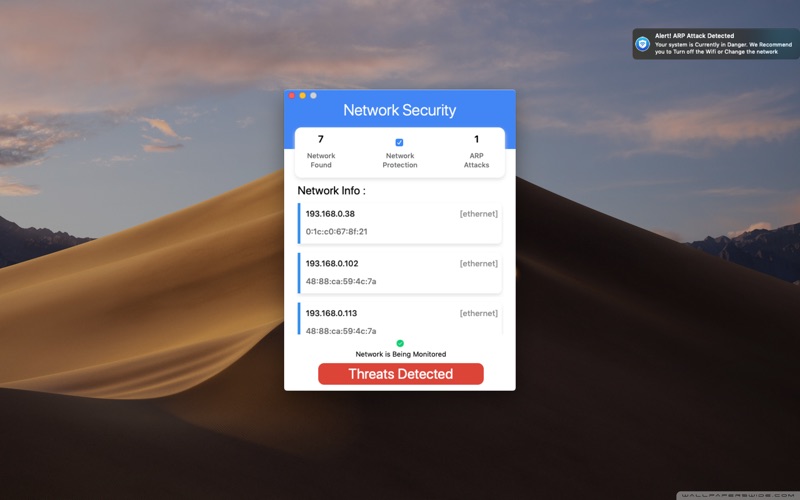
5. Network Security by Max Secure actively monitors your network for ARP or MITM based attacks.
6. Network Protector works in the background and alerts you if there are any attacks or threats detected.
7. It will safeguard your Mac from Man in the Middle attacks that can cause data theft or other attacks on your privacy.
8. This results in the linking of an attacker’s MAC address with the IP address of a legitimate computer or server on the network.
9. Once the attacker’s MAC address is connected to an authentic IP address, the attacker will begin receiving any data that is intended for that IP address.
10. ARP spoofing can enable malicious parties to intercept, modify or even stop data in-transit.
11. It is recommended to use specially when banking, shopping or accessing social networks through WIFI.